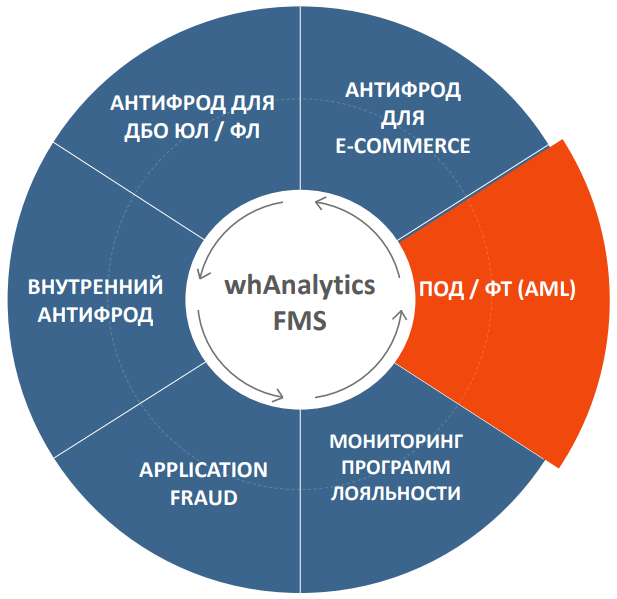
AML
- Home
- AML
// DELIVERY, IMPLEMENTATION AND SUPPORT OF THE DIGITAL SOLUTIONS
Detect suspicious operations
Allows detection of suspicious transactions initiated by the clients and subject to regulatory requirements and the Bank’s internal control rules, providing analytical tools (KYC), the ability to analyze clients’ counterparties through data enrichment from external systems.
- Enrichment with client behavior data from other systems of the company (including non-payment behavior, affiliation) plus external directories, lists, government services.
- Checking the applications online upon their receipt according to a specified set of rules, scoring models and anomaly detection.
- Forming a judgment on an application (group of applications, a client, an agent, a sales point).
- Transfer of judgment to the Company’s executive body (refusal, suspension, investigation).
- Conducting official investigations on fraud or suspicion.
- Modeling the operation of rules and scoring on historical basis.
Extra capabilities
- Black / white / lists creation and maintainance
- Transactions, clients, employee actions scoring
- Rules builder
- Relationship analysis (graph) for all characteristics available for analysis
- Profiling a client’s/employee’s behavior based on transactions, nature of work with accounting systems or IT services, taking into account the role model and client segment. Detecting deviations from the normal behavior profile
- KYC: clients, employees, contractors
- Analysis of an entity’s (client, employee) behavioral characteristics
- Various integration methods
- Use of external reputation databases, blacklists (IP, devices, dropper clients, etc.), the ability to integrate with specialized services
- Capabilities for independent parameterization of rules and reporting
Knowledge base of 100+ fraud detection algorithms
Loss reduction, 95% preventing
Decision making, 5-7times increase in employee efficiency